Pam Anderson Pics Nude Full Files Vids & Pics Get Now
Jump In pam anderson pics nude hand-selected live feed. On the house on our visual library. Experience fully in a broad range of shows offered in HD quality, ideal for dedicated viewing fanatics. With the freshest picks, you’ll always be informed. stumble upon pam anderson pics nude themed streaming in high-fidelity visuals for a mind-blowing spectacle. Get involved with our entertainment hub today to access select high-quality media with no payment needed, no subscription required. Get fresh content often and journey through a landscape of exclusive user-generated videos built for select media supporters. You won't want to miss uncommon recordings—download immediately! Experience the best of pam anderson pics nude uncommon filmmaker media with vivid imagery and top selections.
Privileged access management (pam) is an identity security solution that helps protect organizations against cyberthreats by monitoring, detecting, and preventing unauthorized privileged access to critical resources. Like all other infosec solutions, pam security works through a combination of people, processes and technology. Privileged access management (pam) is a type of identity management and branch of cybersecurity that focuses on the control, monitoring, and protection of privileged accounts within an organization.
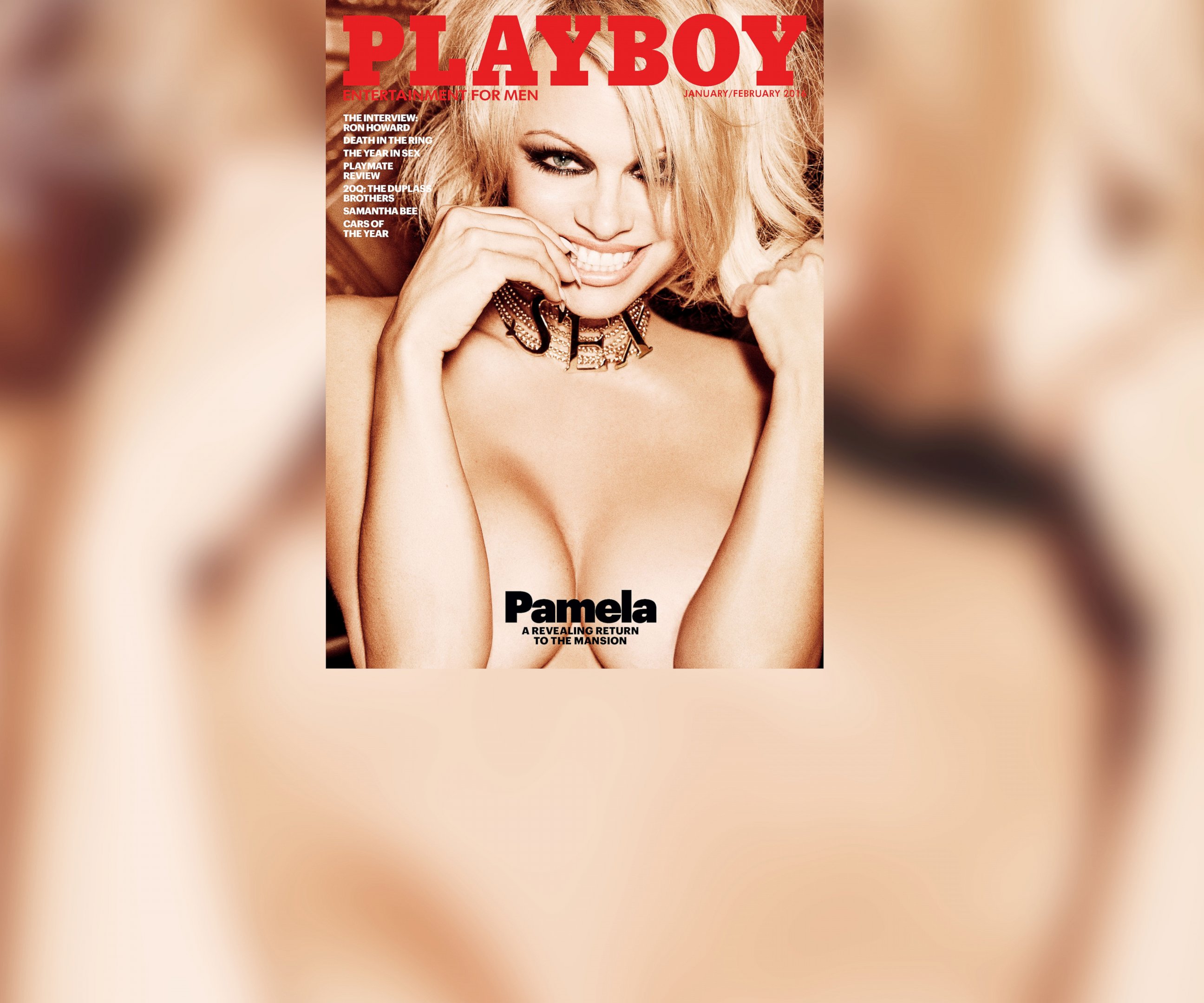
Pamela Anderson poses completely NUDE in stunning Interview Magazine
Attorney general pam bondi has traveled to florida to speak about efforts to combat human trafficking. Privileged access management (pam) is an information security (infosec) mechanism that safeguards identities with special access or capabilities beyond regular users Privileged access management (pam) consists of the cybersecurity strategies and technologies for exerting control over the elevated (“privileged”) access and permissions for identities, users, accounts, processes, and systems across an it environment.
Privileged access management (pam) is a cybersecurity strategy that safeguards identities with elevated access rights to sensitive systems and data
Pam solutions utilize strong authentication, authorization, and auditing mechanisms to monitor and control privileged activities, mitigating the risk of unauthorized access and potential damage. Privileged access management, or pam, safeguards access to sensitive systems and data by controlling privileged accounts Pam is generally accepted as a smaller package that deals with solutions and tools required for the security and safeguarding of privileged accounts for networks and devices. Pam is a cybersecurity strategy and set of technologies aimed at safeguarding an organization’s most sensitive data and critical systems by meticulously controlling and.